LAS VEGAS: At a conference where hackers can try their hand at picking locks and discover cyber vulnerabilities in a makeshift hospital, they can also endeavor to break into the control units of cars and take over driving functions.
Those efforts at the DEF CON security convention in Las Vegas are sponsored by carmakers and suppliers that have increasingly recognized the need to collaborate with so-called white hat hackers — cyber experts who specialize in discovering vulnerabilities to help organizations.
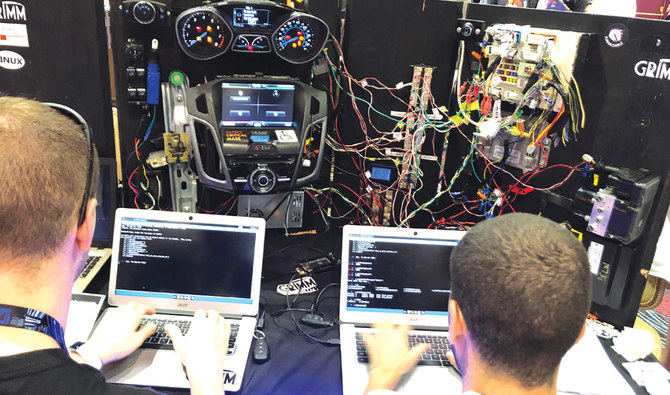
Attendees who visited the car hacking site had to escape a vehicle by deciphering the code to open its trunk, control its radio volume and speed, and lock the doors through their computers.
“A big part of it is redefining the term ‘hacker’ away from that of a criminal to make automakers understand that we’re here to make their systems more secure,” said Sam Houston, senior community manager at Bugcrowd, which recruits researchers for so called bug bounty programs at Tesla Inc, Fiat Chrysler Automobiles NV and other automakers.
Volkswagen AG, Fiat Chrysler and suppliers Aptiv PLC and NXP Semiconductors NV were among the sponsors of this year’s car hacking village — as some have done at previous DEF CON conventions.
Las Vegas once a year becomes the gathering place for tens of thousands of cybersecurity enthusiasts who attend DEF CON and the preceding corporate Black Hat conference.
Weaving their way through revelers at Blackjack tables and beauty salons promising non-surgical face lifts, DEF CON expects at least 25,000 attendees by the end of the weekend.
At DEF CON, the largely male participants are not registered by name to protect their privacy and attendees need to pay in cash to receive a blinking badge featuring an exposed circuit board that allows them to complete tasks.
BACKGROUND
Las Vegas once a year becomes the gathering place for tens of thousands of cybersecurity enthusiasts who attend DEF CON and the preceding corporate Black Hat conference.
The conference provides a rare opportunity for enthusiasts to learn about car hacking.
“Automotive provides a great challenge because the systems are distinct from other security areas,” said Craig Smith, a security researcher who, together with Robert Leale, founded the car hacking village in 2015.
Leale and Smith said they witnessed a steady annual growth in participants.
More connections and technological features in modern vehicles also increasingly attract security professionals from other research areas, said Aaron Cornelius, senior researcher at cybersecurity company Grimm. Cornelius was supervising a station where participants could try to hack into the control units of a 2012 Ford Focus.
Assaf Harel, chief scientist of Karamba Security, a company that provides automotive security technology and works with car manufacturers and suppliers including Denso and Alpine Electronics, said the hacking community has opened the auto industry’s eyes.
“Carmakers have been discovering new issues with their traditional architectures thanks to white hat hackers, which highlighted security needs for carmakers and suppliers alike,” said Harel.
He operated a station where hackers could try to modify a model traffic light.